Archive
EC continues its froth(ing at the mouth) over the NSA
I never cease to be amazed by our politicians – they seem to be incapable of taking a stand and holding a line.
The European Commission is, we are told, furious at the surveillance programs of the National Security Agency. (They are also slightly miffed at those of GCHQ, which is just as bad, if not worse, than the NSA. But GCHQ is British, and Britain is a member of the EU, and the EU cannot, by law, interfere with the security matters of its own members. So that one’s a tad tricky; best keep a low profile.)
But back to the fury at the NSA. In a pit of fique, the EC has declared that if the US doesn’t do what it wants, it might reconsider the safe harbor agreement that allows US companies to export personal European data even though the US is not considered safe to secure it. It won’t, of course. Can you imagine the uproar if Europeans could suddenly not have their hourly fix of Facebook or Twitter or Google mail?
And apart from that, what the EU wants is not for the NSA to stop spying on Europeans, but for Europeans to be able to sue the NSA in the US if it oversteps the mark. Well, good luck with that. A US judge saying that NSA spying on foreigners (perfectly legal, in fact required by law in America) is not legal if that foreigner is European but OK if he is not European? Or perhaps US judges will have to become proficient in European law and adjudicate on EU law for EU citizens living in the EU but spied on from the US? This one will run and run until it is kicked into the long grass and quietly forgotten.
Meanwhile, the EC is keeping quiet over its genuine weapons. Will it stop negotiations on the new ACTA, called the TTIP (Transatlantic Trade and Investment Partnership, not to be confused with – wait, to be totally confused with – the Trans-Pacific Partnership)? Will it hell. A threat like that might actually have an effect.
And what about the Swift agreement – the one that ships European financial data to the US for onforwarding to the NSA? Not a dicky-bird there either.
So, frankly, all this huff and puff from the EC over the NSA spying is pure froth designed to appease the voting public – after all, we’ve got elections coming up in just a few months.
That’s not to say there aren’t some good guys in Europe. An emailed statement from MEP Jan Philipp Albrecht comments, “It is, however, seriously regrettable that the Commission has completely ignored the demand of the European Parliament to suspend the EU-US agreement on the transfer of SWIFT bank transaction data and, instead, delivered a glowing endorsement of the agreement. Revelations that US authorities by-passed the provisions of the agreement, including using cyber-attacks to access SWIFT data, undermine the entire essence of the agreement and cannot be simply left unanswered. This slight by the Commission in ignoring Parliament’s demand must make MEPs more wary in the future about waiving through far-reaching international agreements.”
Sadly, the Albrechts in Europe are massively outweighed by the Camerons in Europe.
Password theory is good – password practice is poor
There’s nothing wrong with passwords. At least there’s nothing wrong with the theory of passwords.
You have a locked room. The only way into the room is through a single door. The only way through the door is with a single key. You have the only key. What’s wrong with that?
Throughout this article we’ll talk about locked rooms and keys. The locked rooms are your accounts, mostly on the internet; and they contain your valuable personal data. The keys are your passwords to those accounts. You should have a separate key for each locked room. If you have a single key for multiple rooms and you lose that key or it is stolen, the finder can get into all of your rooms.
So, just like any key to any room, we have a responsibility to keep it or them safe if we want to keep our property safe. We need to make sure they cannot be guessed; that we do not leave them lying around for others to find; that we make it as difficult as possible for hackers to steal them directly from our desktop computers (anti-virus, firewalls and above all else, common sense); and that we do not make copies and use the same key for multiple rooms (we need a different key for every different room).
The problem is that we hear about new password thefts almost every day. Some of them happen because of earlier password thefts. As soon as your password is stolen, you are no longer the only person who can get into your locked room. Any person who has your password, the key to your locked room, can steal all of your personal, private and valuable information. Here’s a selection of thefts, basically just what I can remember – there’s many, many more – from this year alone:


Criminals get passwords either by knowing them (because they are given them, or they are insufficiently hidden), or they guess them. In the first case they use social-engineering psychology to persuade the user to hand them over (more information on social engineering here, and spear-phishing here), or they find them unhidden by the user. In the latter case they guess the most common passwords, or use automated dictionaries to try every possibility until the right password (key) for a known account (locked room) is found.
Most websites include a limit on the number of failed access attempts allowed within a predetermined period. This means multiple attempts to guess the right password while online are almost certain to fail. That is why criminals steal password databases from websites – so that they can try millions of automated guesses offline without being interrupted. The purpose is still to find the key to gain entry to your locked room, and to steal everything of value within it.
But there’s an easy solution: use complex passwords that cannot be manually guessed, and electronically hide them so that automated guessing still won’t work.
There are two methods for ‘electronically hiding’ text: encryption and hashing. Encryption involves converting text into an apparently meaningless jumble of characters in a manner that can only be unjumbled if you have the secret decryption key – which can be the same as (symmetric encryption) or different to (asymmetric encryption) – the encrypting key for your password. Encryption, by definition, comes with the ability to decrypt – the ability to return the jumble back to the original text. Hashing is different. Hashing is one-way only. Hashing converts the original text into a meaningless jumble that cannot be de-hashed back to the original.
Hashing is the right solution for websites to hide their users’ passwords. It means that even the website doesn’t need to know the password, only the hash, which they cannot return to the original password key. With this method passwords need never and should never be stored by websites.
When you create a new account you are asked to provide a password. That password is hashed, paired with your user ID (often, but not necessarily, your email address), associated with your account, and stored. Whenever you want to access your account, you again enter your password. It is hashed again. If your user ID and the new hash result match with something stored, you are allowed access to the associated account.
Hint: if you forget your password, distrust a website that is able to send you your old password by email – it shouldn’t have your password. The ‘correct’ procedure is to guide you to a place where you can create a new password.
So, the effective use of passwords is a partnership. User’s need to create good passwords and keep them safe, while internet companies need to store them safely and securely. It is my contention that done properly, this will be enough.
Alternatives to the simple password
Before we go too far on the strengths and weaknesses of passwords, we should mention the alternatives.
Passwords are designed to provide user authentication – to prove that Joe Smith really is not just any Joe Smith, but the right Joe Smith. In security terms, authentication is often described by the number of factors it uses – with the implication and a degree of validity that the more factors used, the more secure the authentication. (Personally, I do not believe that is necessarily true.) ‘Factors’ in this sense are things you know (like a password), things you have (like a token), things you are (like a biometric), and so on. The two most commonly used additional factors today are soft tokens and biometrics.
Soft token 2FA
An example of the most commonly used two-factor user authentication is the separate token sent out-of-band to the user’s mobile phone. This is a one-off code. Now you could say that ‘the thing that is owned’ is the separate code, or the phone that it is received on. Either way, the user now requires something he knows (password) and something he owns (phone/token).
I have two problems with this. Firstly, whenever you introduce complexity into security, you also introduce weakness – the phone and the communication sending it can both be attacked separately. The second issue is that this complexity makes it harder to use – and users do not want any more difficulty. If 2FA is an option, most users opt to ignore it. That in itself is not an issue, because we’re back where we started. But the fact that there **is** a 2FA option can mean that users take less care, whether they opt for 2FA or not, simply because it is clear that the vendor is taking more care. There is a danger that 2FA can cause a false sense of security.
Biometric authentication
Biometrics is getting a lot of publicity. Governments use facial biometrics for surveillance and passports; law enforcement uses fingerprints for criminal recognition; and Apple uses finger scans for opening the new iPhone.
I have three concerns. Firstly, nearly all biometrics can be forged. It took researchers just days to break through Apple’s iPhone finger scan. Secondly, what do you do if your biometric is compromised? If your password is compromised, you create or request a new password. What do you do if your iris, or your voice, or your thumbprint is compromised? And thirdly, it’s that old false sense of security – people using biometrics tend to think they are more secure than they actually are.
My contention, which I shall try to demonstrate below, is that passwords – used correctly – are adequate on their own. All we have to do is use them correctly.
Creating secure passwords and keeping them safe
Criminals get into locked rooms by guessing the password key.
When Gawker was breached in 2010, researchers found that the ten most popular passwords were
- 123456
- password
- 12345678
- lifehack [LifeHacker is a Gawker publication]
- qwerty
- abc123
- 111111
- monkey
- consumer
- 12345
When LinkedIn was breached in 2012, researchers discovered that the ten most popular passwords were:
- password
- 123456
- 12345678
- 1234
- qwerty
- 12345
- dragon
- pussy
- baseball
- football
How long do you think it would take to guess passwords like these?
Of course, if the passwords are all held in a single database without any form of electronic jumbling, then a password thief doesn’t need to guess anything because he’s got them written down in front of him. So the websites store the passwords ‘hashed’.
Now the criminals have to start guessing. To help this process, they use computers and specialized dictionaries called rainbow tables. Rainbow tables are effectively long lists of precomputed hash outputs together with the original input text that was used.
Stolen password hashes are then simply compared to the rainbow tables. If the hash output is found, then the password is known – that is, the password has been cracked.
So when you consider a new password, you should also consider how they are cracked with rainbow tables. Any word that appears in a dictionary will be in the tables. Any number up to at least 999,999,999 will be in the tables. All conceivable combinations of letters up to a certain length, and all conceivable combination of letters and numbers up to a certain length, will appear in the tables. In short, if you use a password made up of any combination of letters and numbers up to, say, seven characters, and that password is stolen, you should consider it already cracked and available to the criminals.
This will include some of the commonly recommended methods for coming up with passwords – such as initial letters from quotations. “into the valley of death rode the six hundred” could provide ‘itvodrt600’. That looks like a strong password – but you should assume that it’s in a rainbow table somewhere.
The way to avoid rainbow tables is to use a very long password that mixes uppercase, lowercase, numbers, special characters and punctuation marks. The problem then becomes one of usability – passwords that are difficult to guess are even more difficult to remember.
The best way to produce, store locally and safely, and use strong passwords is to use a reputable and recommended password manager. I’m not going to recommend any myself – you must research that on your own. But the one I use generates passwords for me such as
%wc;I’,;Gp*CfQr9FUFpZYm|
I consider that to be reasonably secure against most tables.
The responsibility of the website
The fact remains that if the vendor doesn’t keep passwords hashed, then it really doesn’t matter how complex I make them.
So if it is incumbent on me to generate strong passwords, then it is equally incumbent on the website to store them securely. That means hashing them.
Actually, it means more than that. It means using a strong hashing algorithm (not all are equally good); it means using a slow algorithm (some were designed for speed when computers were slow, with the unintended consequence of making cracking faster and therefore easier); and they should be salted. Salting is the addition of additional random characters to the user’s password. Basically, salt makes the password even harder to crack – it turns a medium strength password into a strong password.
This is standard best-practice. Unfortunately, too many websites do not conform to best practice. In the last few weeks we have heard:
- Adobe did not hash its passwords; it encrypted them (better than nothing, but not as good as hashing) It also stored users’ password hints next to the encrypted passwords in plain text – making it, in some cases, obvious what the password was.
- LoyaltyBuild stored users’ credit card numbers unencrypted and with the cards’ CVV numbers.
- Cupid Media stored its users’ passwords in plaintext.
What is the point of coming up with a long, complicated, unguessable password if the website just hands it to the criminals on a plate?
Conclusions and recommendations
For password access to locked rooms to work, they need to be strong (from the user) and hashed and salted by the website. Clearly that frequently doesn’t happen; and that’s why we have rampant identity theft.
Since it doesn’t happen voluntarily, we need a new code of practice backed by regulation if necessary. Much of it will fall on the website; but that’s a small price to pay for a secure and trusted internet.
Firstly, websites should require a minimum strength password from their users – so strong, in fact, that it becomes easier to use a password manager than to try to make them up.
Secondly, users must learn not to reuse the same password on multiple sites. Security audits must confirm this as part of staff awareness training, and schoolchildren need it to be taught in schools.
Thirdly, websites must be required, by law if necessary, to make it clear how they protect their users. Inadequate password security could then be shunned by users and ridiculed by professionals.
With these three basic developments, password-protected access will do the job it was designed to do: locked rooms will stay locked, personal and private.
An evolution in the theory of security risk management
Time to rewrite the text books. We have ‘security by threat transfer’, ‘security by threat avoidance’, ‘security by threat reduction’, and ‘security by threat acceptance’.
Now I bring you the latest evolution in the theory of security risk management: security by denial…

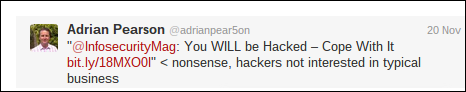

This, ladies and gentlemen, is why we have a problem.
Adobe – you really cocked-up on this one
I finally got the email I’ve been waiting for. It’s from Adobe. It starts
As we announced on 3 October 2013, we recently discovered that an attacker illegally entered our network and may have obtained access to your Adobe ID and encrypted password. We currently have no indication that there has been unauthorised activity on your account.
To prevent unauthorised access to your account, we have reset your password…
Let’s have a look at this. “We announced on 3 October 2013, we recently discovered…” What does recently mean? They announced on 3 October not because they had discovered the hack, but because Brian Krebs told the world that he had found stolen Adobe data on the internet. So when it was actually stolen (could have been months earlier) and when Adobe actually became aware of the theft (could have been months earlier) is not known.
Let’s be charitable and say Adobe knew about it by 1 October.
They said that just under 3 million usernames and encrypted passwords may have been stolen. Since I don’t have an Adobe account, and since 3 million is relatively few in the overall scheme of things, I thought no more about it.
A few weeks later Adobe admitted that the true figure is nearer 38 million. That’s getting a bit more worrying, so I checked my browser’s stored passwords and my more recently adopted password manager. Still nothing. No Adobe account. And anyway, Adobe said very clearly that the company had reset all the passwords and notified the 38 million users. I had not been notified. I had nothing to worry about.
But then, about a week later, it emerged that it wasn’t a mere 3 million, nor a more worrying 38 million, but a colossal 150 million. Adobe had notified 38 million out of 150 million – but that is by no means the worst of it. When Paul Ducklin got hold of the database of stolen data, now easily available if you know where to look, a quick analysis showed the user’s email in plaintext, an encrypted password, and the user’s password hint in plaintext.
email addresses – you can infer a lot from an address: usually the user’s name and company. For example, Ken Westin at Tripwire looked through the Adobe hack and found 89,997 military addresses. “This is in addition to the more than 6,000 accounts from defense contractors such as Raytheon, Northrup Gruman [sic], General Dynamics and BAE Systems we also found,” he wrote. “Also, on the federal side, there were 433 FBI accounts, 82 NSA accounts and 5,000 NASA accounts.” So, choose your company, guess the user’s name, look through LinkedIn and Facebook and you’ve got enough for a pretty compelling targeted phishing attack.
encrypted passwords – passwords should be hashed and salted with a slow hashing algorithm; they should not be encrypted. Hashing means 150 million passwords need to be cracked; encryption means that one key needs to be cracked and all 150 million passwords are known.
password hints in plaintext – oh, really! Why bother cracking the passwords when the hint will let you guess it? What do you think is the password when the hint is ‘57’; or ‘the bad disciple’?
So Adobe really cocked-up. They didn’t protect the data, they didn’t store it correctly, and they tried to minimise the extent of the damage. And still it gets worse; because they tried to suggest, don’t worry, most of these accounts aren’t real, they belong to people who just signed up to get promotions or freebies.
Here’s the real danger. In that great mass of one-off freebie-chasing accounts numbering anything between 38 million and 150 million are people who signed up, used a password that they can’t remember, and are completely unaware that their password is now compromised. What if these people signed up years ago before password thefts became a dime a dozen, and lazily used the same password as they use on their email address? There is no way that they can retrieve that password. They now have no way of knowing whether any or which or all of their other accounts have been compromised by Adobe’s failure to adequately protect this password.
One final point. I said at the beginning that I had been expecting the email from Adobe. That’s because I checked with LastPass (who has a little routine that will tell you whether you’re included in the hacked data) and learnt that although I couldn’t ever remember creating an Adobe account, at some point I must have done, because there I was.
So, at least six weeks after it knew of the breach, Adobe bothers to tell me that someone “may have obtained access to [my] Adobe ID and encrypted password” when the world and his dog has access to that encrypted password. I know; Ken Westin, Brian Krebs and Paul Ducklin almost certainly know; LastPass and the hackers most definitely know; and anyone who cares to look will also know. Adobe, however, doesn’t know and continues to insist that ‘an attacker… may have obtained access.”
How dare they, after all this time and all these mistakes, still try to save face at my expense?
Trust and the Internet
Wonderful idea from Deutsche Telekom. Yesterday it said it would launch a clean pipe secure service for small companies that cannot afford their own security. For a fixed monthly fee small companies will be able to access the internet via DT’s own secure data centres. “Hackers will have no chance,” said management board member Reinhard Clemens. Well, we’ll just gloss over that, and accept it at face value.
“The ‘clean pipe’ project, in which Deutsche Telekom partners with RSA – part of U.S. technology firm EMC – is in a test phase and scheduled to hit the market early next year,” reports Reuters.
So, just a little due diligence required before I sign up…
OK, Deutsche Telekom owns T-Mobile. T-Mobile “operates the fourth and fifth largest wireless networks in the U.S. market with 45 million customers and annual revenues of $21.35 billion.” (Wikipedia). Slight problem; that means that T-Mobile is subject to FISA in the US – and the US gets DT more than $20 billion.
OK, RSA is a huge name in encryption. That’s got to be good (even though it is, well, yes, an American company). RSA got big and very rich on its invention of public key cryptography. Thing is, RSA didn’t invent it – it was invented by Ellis, Cocks and Williamson at GCHQ.
Now the details are rather obscure and still shrouded in secrecy, but there are suggestions that GCHQ told the NSA what it had discovered, and shortly after that, public key cryptography was (re)invented in the US.
I would not for one moment suggest anything underhand in the timing – but given what we now know about both the NSA and GCHQ there is a temptation to ask whether public key cryptography would have been allowed to develop if the very same mathematicians who produced it had not also discovered a way to unpick it.
Mathematicians and cryptographers tell us that cryptography based on the difficulty in factoring large nearly primes is valid.
But…
And that’s the point. But.
Thank you NSA. Thank you GCHQ. You have reduced a wonderful and exciting internet into something dirty and distrustful. Thank you for removing any possibility of trust anywhere.
The truth is out there – it’s just not in the newspapers
Blogs are different to newspapers. You can get away with greater subjectivity in a blog than you can in a newspaper. But newspapers cannot absolve themselves of their responsibility for pure objective fact by calling a particular section a blog.
So when Martha Gill wrote about Anonymous in the Telegraph blog, it was wrong. Her headline says it all: Anonymous have been exposed as hypocrites. Watch them try to wriggle out of it (6 November 2013). You can hear the glee in her voice – this is personal, not factual.
Anonymous responded with an open letter to the media in general. It accused Gill of being inaccurate in one of her two accusations (that their masks are produced in what she strongly implies is a sweatshop) and hypocritical in another (that Warner Bros benefits from every sale of a mask). On the latter, Anonymous suggests that royalties are a sad fact of life; and wonders how many Telegraph staff support Foxconn by using Apple or Dell, Sony or HP equipment. “Since 2010, at least 17 deaths occurred when employees committed suicide by jumping from the roof of the building. To use a phrase from Martha Gill’s article, these are certainly ‘unpleasant conditions.’”
But in reality, this incident is just a small local battle in a much larger war. Anonymous – and it’s not alone – believes that much of the media has been bought and usurped by government and big business; and supports the agenda of government and big business to the exclusion of truth. It is no coincidence that there is a nationwide (US) march against corporate media planned for next Saturday:
We are planning a march and rally in Washington DC to raise awareness of the privatization, corporatization, and monopolization of the mainstream media and the corruption of our fifth estate. The failure of the corporate networks to adequately cover critical social issues has allowed for the rampant corruption of our political and economic system to go unquestioned and unchallenged.
March against mainstream media
If you have already thought about this, it cannot be denied. A few (very few) newspapers have kicked back in recent months with the Snowden revelations (notably the Guardian, Washington Post and Der Spiegel); but it’s also noticeable that the Guardian is under threat of prosecution in the UK for doing so.
And if you want a specific current example of this media betrayal, consider an EFF blog from Thursday: How Can the New York Times Endorse an Agreement the Public Can’t Read?
The New York Times’ editorial board has made a disappointing endorsement of the Trans-Pacific Partnership (TPP), even as the actual text of the agreement remains secret. That raises two distressing possibilities: either in an act of extraordinary subservience, the Times has endorsed an agreement that neither the public nor its editors have the ability to read. Or, in an act of extraordinary cowardice, it has obtained a copy of the secret text and hasn’t yet fulfilled its duty to the public interest to publish it.
TPP is the successor to ACTA. ACTA was defeated by European activism. It is dead. TPP allows the same provisions to be established everywhere else without European involvement. Once this is achieved, the new discussions on an EU/US trade agreement will be dragged into the same agreements – it will be inevitable.
But where is the mainstream media’s concern over either? In defeating ACTA, the people made it very clear that they do not want ACTA – more specifically the internet-controlling, copyright-enforcing aspects of it. To understand the great Battle of ACTA, read Monica Horten’s new book, A Copyright Masquerade.
Rather than accept the will of the people, big business and government withdrew, regrouped, renamed and returned from a different direction, calling it TPP and being equally if not more secretive.
The problem is that the mainstream media is not on the side of its readers, but on the side of its owners.


Quite simply, the majority of US news outlets are owned by the same media companies that are lobbying in favour of trade agreements that will take over control of what appears on the internet, who can see what, and who goes where. Quite frankly, we can no longer believe what we read in the press any more than we can believe what government tells us.
Bits of Freedom seeks clarity from the AV industry on collusion with law enforcement
On 25 September I posed the question: Is the anti-virus industry in bed with the NSA? Now Bits of Freedom, a Dutch digital rights group, has asked the same question in a letter signed by more than 25 civil rights groups and individuals (including Bruce Schneier, EDRi and EFF).
On 25 October it wrote to more than a dozen of the world’s leading anti-virus companies asking four specific questions:
1. Have you ever detected the use of software by any government (or state actor) for the purpose of surveillance?
2. Have you ever been approached with a request by a government, requesting that the presence of specific software is not detected, or if detected, not notified to the user of your software? And if so, could you provide information on the legal basis of this request, the specific kind of software you were supposed to allow and the period of time which you were supposed to allow this use?
3. Have you ever granted such a request? If so, could you provide the same information as in the point mentioned above and the considerations which led to the decision to comply with the request from the government?
4. Could you clarify how you would respond to such a request in the future?
With the greatest respect, this is a pointless exercise; the companies will deny any collusion with law enforcement to subvert their products whether they have or not. And they may have, or they may not.
I have no idea whether there is collusion between AV and law enforcement. Every single member of the AV industry I have spoken to denies it absolutely – and I believe them. There really are some great, learned, honest and honourable guys in the AV industry. But the NSA says it doesn’t break the law; and I absolutely do not believe them.
We know that the NSA hacks into third-party computers and installs malware. We know that it is the AV industry’s job to detect and neutralise such malware. We therefore know that the NSA will not want the AV industry to do that to their own malware.
It would be easy enough to defeat AV engines to get onto a computer; but it is less easy to stay hidden for any length of time after that. But we know that state-sponsored malware remains undetected for years. How does it do that? The easiest way would be to subvert the seek and destroy software that hunts it.
So, given the amount of time and resources that the NSA has spent on subverting what gets in its way – such as encryption – is it reasonable to believe that it hasn’t spent similar effort on neutralizing the AV industry?
I don’t know the answer; and it doesn’t matter who in the AV industry tells me, nor in what regard I hold them, nor how many times they tell me, I still will not know.
And that, perhaps, is the very worst thing that the NSA has done. It has destroyed trust in the internet, and has destroyed trust in anything to do with the internet. For that the NSA cannot – and must not – ever be forgiven.
It is time for Brits to realise that they cannot trust their government
If you are suffering from ‘shock fatigue‘ (and who isn’t?) over the never-ending revelations on the extent and degree of NSA surveillance on all of us, then I can do no better than recommend you view NSA Files: Decoded – What the revelations mean for you. It is a single document that provides an overview of what we’ve learnt so far, and is interspersed throughout with brief videos on viewpoints from both sides of the fence.
If you are American, then you should be proud of the public debate that these revelations have prompted. If you are British, you should be worried about the lack of any public debate at all.
Britain’s spy agency GCHQ has secretly gained access to the network of cables which carry the world’s phone calls and internet traffic and has started to process vast streams of sensitive personal information which it is sharing with its American partner, the National Security Agency (NSA)…
“It’s not just a US problem. The UK has a huge dog in this fight,” Snowden told the Guardian. “They [GCHQ] are worse than the US.”
Guardian, Friday 21 June 2013
But where is the public debate in the UK? It doesn’t exist.
To understand why, you have to consider the nature of the two countries. America was founded on a distrust of government (ironically, specifically the British government). Protection against government authority is built into the American Constitution. And to this day, Americans instinctively distrust big government.
Britain is different. Its democracy has grown slowly and peacefully over a thousand years. Brits instinctively believe that their government is good; Brits instinctively trust big government.
The result of Snowden’s revelations is that both governments are trying to justify their surveillance practices; but while the American government is on the defensive, the British government is decidedly offensive.
Meanwhile, in Britain, prime minister David Cameron accused the Guardian of damaging national security by publishing the revelations, warning that if it did not “demonstrate some social responsibility it would be very difficult for government to stand back and not to act”.
NSA Files: Decoded
Meanwhile, in Britain, government agents forced the physical destruction of the Guardian disks containing Snowden files:
The intelligence men stood over Johnson and Blishen [Guardian staff] as they went to work on the hard drives and memory chips with angle grinders and drills, pointing out the critical points on circuit boards to attack. They took pictures as the debris was swept up but took nothing away.
NSA files: why the Guardian in London destroyed hard drives of leaked files
Meanwhile, in Britain, Glen Greenwald’s boyfriend David Miranda was detained at Heathrow for 9 hours and had his computer equipment confiscated because he was suspected of being a terrorist:
At the time I said that all the police had to do was justify the suspicion that Miranda was a terrorist as defined in the Terrorism Act; which would be easy.
Britain: the Miranda detention proves it is a police state in action
Meanwhile, in Britain, an emergency debate in Parliament did not discuss GCHQ overreach, but instead discussed the Guardian’s support for terrorists:
This debate, however, focuses on a narrower and darker issue: the responsibility of the editors of The Guardian for stepping beyond any reasonable definition of journalism into copying, trafficking and distributing files on British intelligence and GCHQ. That information not only endangers our national security but may identify personnel currently working in our intelligence services, risking their lives and those of their families.
Parliamentary debate: National Security (The Guardian)
Incidentally, Paul Flynn (a Labour MP) attempted a ‘point of order’:
On a point of order, Mr Caton. You are the guardian of the reputation of this debate, and so far it has demeaned Parliament’s reputation, because we have had two speeches that were written and read with no attempt to engage us in debate. This is McCarthyite scaremongering that disgraces Parliament.
Meanwhile, in Britain, the government’s pet poodle paper (The Daily Mail, if you hadn’t guessed) attacked the Guardian:
Stupendous arrogance: By risking lives, I say again, the Guardian is floundering far out of its depth in realms where no newspaper should venture…
Stephen Glover, 9 October 2013
Put quite simply, the British government has very successfully managed to turn attention away from its surveillance programmes and against, instead, the newspaper that exposed it. The message is irrelevant, it suggests — it is the messenger that should be shot.
It is time, I suggest, for the British people to understand that its government cares not a jot for the British people, nor for democracy, nor freedom, nor liberty. It cares more for secrecy; and demands to be left alone to carry on unchecked. It is time for Brits to learn to distrust their government.
Britain: the Miranda detention proves it is a police state in action
It usually gives me great and smug pleasure to be able to say, “I told you so”; and this blog has done that on a few occasions. This time it gives me no pleasure – and I’ll come to that later.
David Miranda was detained at Heathrow airport for 9 hours, and his computer equipment confiscated by the Metropolitan Police. There was huge concern voiced by civil liberties groups; and a judicial review was launched.
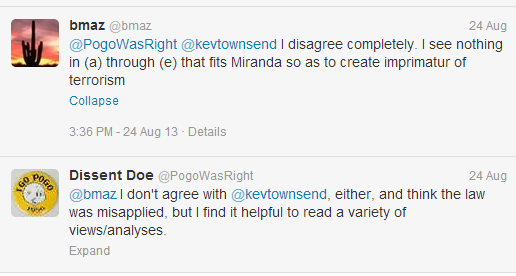
At the time I said that all the police had to do was justify the suspicion that Miranda was a terrorist as defined in the Terrorism Act; which would be easy. I was taken to task on Twitter by bmaz:


What I said was this:
…and assuming that his laptop contained Snowden documents (which would be reasonable suspicion),
- the stated purpose of the leaks is to influence government
- the stated purpose could be described as both ‘political’ and ‘ideological’
- the effect, according to government, could result in increased terrorist attacks against the UK (that is, “a serious risk to the health or safety of the public”) and is also designed “to interfere with or seriously to disrupt an electronic system” (that is, GCHQ’s Tempora surveillance system).
I think it is quite clear that under the Terrorism Act, David Miranda is a terrorist.
Yesterday, Saturday, the Guardian quoted from the police documents referred to in the judicial review. The final Port Circular Notice – the document used by the police to justify Miranda’s detention – includes the following paragraph:
We assess that Miranda is knowingly carrying material, the release of which would endanger people’s lives. Additionally the disclosure or threat of disclosure is designed to influence a government, and is made for the purpose of promoting a political or ideological cause. This therefore falls within the definition of terrorism and as such we request that the subject is examined under schedule 7.
Well, I told you so. But this time it gives me no pleasure to say so, because it confirms my final statement in that post:
“This is a police state in action; and the Terrorism Act is one of its tools.”
see also: Was David Miranda’s detention a legal and reasonable application of the Terrorism Act?