Archive
Is it safe to carry on using Dropbox following the DMCA takedown revelations?
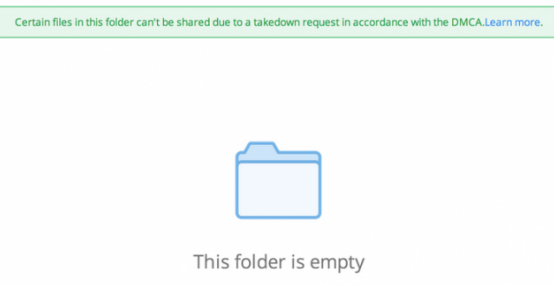
Over the weekend, Darrell Whitelaw tweeted a Dropbox error message that said certain files could not be shared due to a DMCA takedown request.


The immediate concern was that perhaps Dropbox files are neither as safe nor private as its users had thought — how could Dropbox take down files if it did not scan the users’ folders?
In fact, Dropbox is being rather clever. Its problem is this: Dropbox is primarily used as a file syncing system, allowing users to transfer files from one personal device to another personal device. If the user owns or has licensed the files in question, this is not generally a problem.
In fact, from 1 June 2014, UK copyright law will be changed to explicitly allow consumers to make additional copies of copyrighted works for personal use — so transferring music from the tablet you used for downloading, via Dropbox, to the PC you will use to burn CD for playing on your music centre will be perfectly legal.
But as a US company, Dropbox is also subject to the peculiar effects of the DMCA. Under this law, rightsholders can simply demand that copyrighted materials should be taken down. While the service provider can challenge this, failure to respond to a valid takedown demand can prove very expensive. As a result, in many cases the receipt of a DMCA takedown request automatically triggers its takedown without any further query.
It is in trying to balance these apparently contradictory pressures that Dropbox has developed a rather sophisticated solution. If we look more closely at the error message wording, we can see it says that ‘certain files can’t be shared’ because of a valid DMCA takedown request. But it also says that the folder is empty.
The files themselves have not been taken down; it’s just that public sharing has been blocked — that is, this folder is empty for this user, but not for the owner. In other words, Dropbox does not takedown legally owned or licensed files; but it does prevent them being illegally shared to other people.
This just leaves the second concern: how does Dropbox know what is in the folder unless it scans it?
In fact, it doesn’t know — or at least it doesn’t necessarily know. When files are first uploaded by the user, they are hashed. This is automatic and doesn’t require Dropbox to know anything about the file itself. The hash algorithm generates unique fixed length outputs from variable length inputs. Dropbox stores these hashes.
Elsewhere is a separate database of different hashes produced from files that have been subject to successful DMCA takedowns. Whenever a user publicly shares a file that has been uploaded, Dropbox compares its own hash to that on the takedown list. If there is a match, Dropbox blocks the public sharing. It doesn’t need to scan the folder, nor even know what the file is.
Dropbox is thus using best efforts to comply with US copyright laws, accommodate European laws, and maintain user privacy. It’s not foolproof, of course, because the user could encrypt the file locally before uploading it. The resulting hash would then not match any other hash.
Well, that’s the theory, anyway. In reality, Dropbox will know many of the files stored by users via the separate database of hashes. But this then provides the potential for different privacy abuses — user profiling based on music and video tastes, for example.
At the same time, repeated encryption of movie-length files prior to uploading could act like a red-flag and draw the attention of The Eye. That in itself would probably be enough to trigger a Patriot Act NSL demanding the user’s details without allowing Dropbox to tell anyone about it.
So, basically, as we always say about Dropbox… is it safe to use? Yes… and no.
Philips SmartTV susceptible to hack and hijack
A firmware update to the Philips SmartTV delivered last December introduced a vulnerability that leaves it open to hackers. The problem lies in a feature called Miracast. Miracast allows other devices to connect to the TV via wifi.
The problem, however, is that it uses a default hard-coded password that the user cannot change: miracast.
Maltese researchers ReVuln published a video on how to exploit the vulnerability.


In a short associated note, they added,
The impact is that anyone in the range of the TV WiFi adapter can easily connect to it and abuse of all the nice features offered by these SmartTV models like:
- accessing the system and configuration files located on the TV
- accessing the files located on the attached USB devices
- transmitting video, audio and images to the TV
- controlling the TV
- stealing the browser’s cookies for accessing the websites used by the user
In short this vulnerability could provide access to a user’s current email session for anyone within range of the wifi signal. It would also allow pranksters to hijack the TV and play inappropriate content to inappropriate viewers at inappropriate times — or perform phishing scams/adverts direct to the screen.
In reality it will not be difficult for Philips to get rid of the Miracast flaw with another firmware update doing away with the hard-coded fixed password (although a directory traversal flaw also needs to be fixed), but it should serve as a reality check for the future of the internet of things. As more and more devices in both the home and office become interconnected and interdependent, the volume of these vulnerabilities will increase. And with the flaws will come the criminals.
Manufacturers who have never had to consider infosecurity in the past, must now start considering it at the design phase. “What these vendors do not realise,” said Lancope CTO, TK Keanini in an emailed comment, “is that if they don’t build in automatic updating they are not going to succeed and worse, they will be making their consumers’ networks more insecure as updating and patching these flaws post purchase is incredibly difficult, even for the most tech savvy household. The first vendor to deliver devices that can automatically update and adapt to the changing threat environment will be the leader.”
Android malware is no longer just about premium rate calls
Experts have been warning for some time about the increasing sophistication of mobile malware. Now FireEye has discovered a new variant of Android.MisoSMS — which was already an advanced information-stealing Android Trojan.
Like the original version of the malware, the new variant sends copies of users’ text messages to servers in China. But the newest rendition adds a few features that make it harder to detect, including a new disguise, encrypted transmissions, and command-and-control (CnC) communications that are handled natively rather than over email.
FireEye — Android.MisoSMS : Its back! Now with XTEA
The latest variant seeks to communicate with its C&C server — still located in China — via a selection of hardcoded public DNS servers. This helps defeat sandbox detection and analysis since sandboxes “typically use internal DNS servers and cut off access to outside networks,” explains FireEye. “If the malware cannot access the hard-coded DNS servers, it does nothing and is therefore not detected.”
A further new sophistication is the use of encryption — a variant of the XTEA encryption algorithm — in communication with the C&C server. It is clear that it is malware designed to infiltrate and persist.

It suggests, warns FireEye, “that cyber attackers are increasingly eyeing mobile devices — and the valuable information they store — as targets. It also serves as a vivid reminder of how crucial protecting this threat vector is in today’s mobile environment.”
Let’s not forget Assange
(From a translation of a television interview broadcast in Sweden between Eva Joly and Malou von Sivers; available here.)
Eva Joly, a French-Norwegian prosecutor — famous in France for spending 8 years on a corruption case that ultimately convicted 33 of 36 people involved in a massive petrochemical corruption case — is in Sweden to see if she can break the deadlock over Julian Assange. Her concern is neither to prove his innocence nor prove his guilt; only that the current impasse is broken and that the case is either tried or dropped.
It has to be said that she is being met by a judicial brick wall.
Her position is that there is no need for the current situation — Assange could easily be interviewed in London, and even tried while he remains in London.
I’ve been in precisely this situation: I have a suspect who is in another country and doesn’t want to return to France to be questioned. So then I travel with the assistance of the country he’s in and question him there. This is a very common situation. What I think is uncommon is that the prosecution authority in Sweden refuses to use this opportunity, especially after 2000 when we have very good judicial cooperation in Europe. So to travel and question Julian Assange at Ecuador’s embassy in London is no big deal.
But the Swedish prosecutor refuses to do this — and you have to wonder why.
So? Where is the risk to Assange in going back to Sweden to face trial? After all, the Swedish prosecutor Marianne Ny has said there is no chance of Assange being extradited to the US.
When Marianne Ny says he won’t be turned over to the US, she is talking about things where she has no competence. She knows nothing about this.
The reality is that since the year 2000 there has not been a single incidence of Sweden refusing to act on a US extradition request. Assange would be a big catch for the US, and Joly has little doubt over what would happen.
Do you remember how Snowden fled to Moscow? And Eva Morales was in Russia and he traveled back to Bolivia. There were rumours that Snowden was on board his airplane. And what happened then? All the countries of Europe closed their airspace. France closed her airspace, and Morales’ airplane was forced down in Austria. The plane was searched to see if Snowden was on board. There you can see what resistance the countries of Europe have against the US. We were the victims of the surveillance Snowden revealed, we know that French politicians were being spied on, Angela Merkel was being spied on, and still and all France, a nuclear power, who can stand up to the US, they lay down flat for the US demand to get Snowden. Now what do you think would happen if that demand were about Assange? I don’t think there’d be much resistance.
So Joly is in Sweden — an experienced European prosecutor seeking to expedite a fair trial for Assange, because she wants “the case to move along because it is a human right to be tried in a reasonable time.” She has the knowledge of European law and the understanding of an experienced European prosecutor to show how this could be achieved — so you would expect the Swedish authorities to be keen to talk. But no.
I asked to meet with the Minister for Justice, she didn’t have time, I asked to meet with the Prosecutor-General, he referred me to Marianne Ny… and she didn’t want to meet with me. So I haven’t had any luck with the justice system. But that’s OK. Those are their decisions. Now I’m going to speak with the leader of the Parliamentary Judicial Committee, the leader of the Swedish Bar Association, because this is truly an issue of human rights, and I think this situation, which the Swedish judicial system is today responsible for, this hurts Sweden’s reputation.
Quite frankly, if Sweden wishes to prosecute Julian Assange and there are ample ways this can be done while recognising his legal right to asylum in Ecuador, and yet Sweden absolutely refuses to do this, then you have to assume that there is more to this than just a simple accusation of rape. There can be no doubt that Julian Assange’s fears are absolutely correct, and that the accusations against him are being manipulated by a Swedish/American conspiracy to get him extradited to the US for trial on espionage charges.
The threat of the petroruble
Little snowballs at the top of a hill start so small — but if left to roll unfettered, over time they can grow large enough to flatten anything in their path. Putin has pushed a little snowball off the top of the hill.
One bank in Russia has decoupled itself from the dollar. It started with US sanctions over Crimea; but it has allowed Putin to enforce all trading via the Rossiya bank to be conducted in rubles — from consumables to oil. Did I say oil? I’m afraid I did — and this could be the beginnings of the petroruble.
It is the petrodollar that has kept the US — which consistently spends more than it earns — afloat for years. So long as the world’s oil is traded in dollars and world demand for dollars is maintained for that purpose, then the US can simply keep printing more money to pay for whatever it wants. Without that demand, the US economy would be in serious trouble.
So serious, in fact, that when Iraq (with the second largest oil reserves in the world) threatened to stop trading its oil in dollars and start using the Euro, the Bush response was to invade Iraq and impose a more friendly regime.
Russia, like Iraq, is an energy country.
The petroleum industry in Russia is one of the largest in the world. Russia has the largest reserves, and is the largest exporter, of natural gas. It has the second largest coal reserves, the eighth largest oil reserves, and is the largest producer of oil.
Wikipedia
If the rest of Russia follows the Rossiya bank and switches to all energy trades in rubles, then that’s a serious issue for America. If other oil companies aligned with Russia (for example, Iran and Venezuela) also dump the dollar for the ruble for oil trades, it escalates beyond serious. It could be catastrophic.
Let us all hope that the US response to the threat of Russia abandoning the dollar is not the same response it had for Iraq’s threat to abandon the dollar.
Update on the Target/Trustwave suit: Trustwave will vigorously defend its corner
On Friday I reported on the complaint against Trustwave over the Target breach. I criticised Trustwave for both assessing and then monitoring Target. This was an assumption based on the court documents, which state:
Trustwave scanned Target’s computer systems on Sept. 20, 2013, and told Target that there were no vulnerabilities in Target’s computer systems. Trustwave also provided round-the-clock monitoring services to Target, which monitoring was intended to detect intrusions into Target’s systems and compromises of PII or other sensitive data. In fact, however, the data breach continued for nearly three weeks on Trustwave’s watch.
In fact Trustwave did not monitor Target’s networks. CEO Robert J. McCullen yesterday issued an open letter to customers. He said that the lawsuit is without merit, and “we look forward to vigorously defending ourselves in court against these baseless allegations.”
Contrary to the misstated allegations in the plaintiffs’ complaints, Target did not outsource its data security or IT obligations to Trustwave. Trustwave did not monitor Target’s network, nor did Trustwave process cardholder data for Target.
A Letter To Our Valued Customers — Robert McCullen
Britain: a land of censorship by omission
Let’s all try a little experiment.
Index on Censorship warned today about what it calls ‘censorship by omission’ in the UK. The suggestion is not that the British are told what to think by the UK press, but that they are controlled over what they are allowed to think about. It suggests that serious news can be omitted from print while newspapers guide their readers to less important, or even old, news.
The British news spectrum was recently obsessed with Labour politicians Harriet Harman and Patricia Hewitt, who worked for the National Council for Civil Liberties (now ‘Liberty’) in the 1970s. That council granted affiliate status to the now-banned Paedophile Information Exchange (PIE). The Daily Mail made a huge splash about its PIE investigation in February, despite uncovering no new information. That paper alone had reported the same story in 1983, 2009, 2012 and 2013. Eventually the BBC, online world and print media all covered the controversy, meaning more worthy issues lost precedence.
British news blind spots: Omission and obscurity
The result, warns Index on Censorship, is a form of censorship by omission:
We’re denied investigation or campaigning on vital issues because nobody knows they exist.
So here’s our experiment. Let’s see over the next few days just how much coverage we get on the Snowden files released today by Der Spiegel. Quoted by Glenn Greenwald’s new publication, The Intercept, this includes:
One undated document shows how British GCHQ operatives hacked into the computer servers of the German satellite communications providers Stellar and Cetel, and also targeted IABG, a security contractor and communications equipment provider with close ties to the German government. The document outlines how GCHQ identified these companies’ employees and customers, making lists of emails that identified network engineers and chief executives. It also suggests that IABG’s networks may have been “looked at” by the NSA’s Network Analysis Center.
The ultimate aim of GCHQ was to obtain information that could help the spies infiltrate “teleport” satellites sold by these companies that send and receive data over the Internet. The document notes that GCHQ hoped to identify “access chokepoints” as part of a wider effort alongside partner spy agencies to “look at developing possible access opportunities” for surveillance.
In other words, infiltrating these companies was viewed as a means to an end for the British agents. Their ultimate targets were likely the customers. Cetel’s customers, for instance, include governments that use its communications systems to connect to the Internet in Africa and the Middle East. Stellar provides its communications systems to a diverse range of customers that could potentially be of interest to the spies – including multinational corporations, international organizations, refugee camps, and oil drilling platforms.
Der Spiegel: NSA Put Merkel on List of 122 Targeted Leaders
So let’s be very clear here. This is a direct accusation that GCHQ has been hacking into the telecommunications products of friendly companies in allied nations. Over the next few days it will be worth seeing just how much coverage this very major, very important story actually generates in the British mainstream press.
Here’s my prediction — and I genuinely hope I am proved very wrong: there will be serious coverage in the Guardian and Independent (read by very few who don’t already know that GCHQ is hack-crazy and law-breaking); some coverage in the Telegraph (read by hardly anyone); dismissive, brief coverage by the BBC; and preciously little else.
Let’s see.
PCI DSS auditing — Jesus wept
At first I thought 1st April had come early. Now I’m not sure. Either way it’s hilarious, and if you want a good laugh, please read: Our security [PCI DSS] auditor is an idiot. How do I give him the information he wants?
But after the laugh, have a good weep. These are the people who declare the systems that handle our credit cards to be secure — or not.
In a nutshell, this auditor demanded all his client’s passwords in plaintext. Hey, wait a minute, said the client, and wrote back:
Unfortunately there is no way for us to provide you with some of the information requested, mainly plain-text passwords, password history, SSH keys and remote file logs. Not only are these things technically impossible, but also being able to provide this information would be both against PCI Standards, and a breach of the data protection act.
The auditor replied
As explained, this information should be easily available on any well maintained system to any competent administrator. Your failure to be able to provide this information leads me to believe you are aware of security flaws in your system and are not prepared to reveal them. Our requests line up with the PCI guidelines and both can be met. Strong cryptography only means the passwords must be encrypted while the user is inputting them but then they should be moved to a recoverable format for later use.
That was my emphasis, but the client comments, “I’m going to frame that and put it on my wall.”
Now that we’ve all had a good laugh, the reality can set in. This auditor has the power of declaring a client who stores passwords in ‘a recoverable format’ to be ‘secure’. No wonder we have so many hacks.
Microsoft’s new secret weapon: listening to its customers
I am not Microsoft’s greatest fan. It is a dinosaur stuck on the beach while the fleeter of foot are soaring through the clouds. The reality is that it has no, and has never had, any visionaries. Even its domination of the desktop was more down to luck and sharp practices than genuine vision.
It was lucky that Gary Kildall rejected IBM’s overtures, else there would never have been an MS-DOS; and it was sharp practices that killed off Digital Research — its one serious and technically superior competitor. It was lucky that Apple demonstrated the value of Xerox Parc research and paved the way for Windows. It was lucky Jobs was so far ahead of his time he thought he could have a walled garden in the ’80s; and almost destroyed Apple in the process.
But it was sheer arrogant blindness that made Gates think he could ignore the internet. For the last two decades Microsoft has been forced into playing catch up; but catch up never works if you don’t have the vision to get ahead of the competition.
Now, in just one area, Microsoft is showing visionary signs that could differentiate it from all of its competitors. Microsoft has started listening to its customers rather than imposing its will on its customers.
While Facebook is telling everyone that they don’t want privacy, Microsoft is listening and saying, OK, we will give you privacy. While Google is fighting the European Union over privacy and cloud storage, Microsoft is listening to the EU and saying, OK, we can accommodate and store European data in European data centres.
Now, it’s not as simple as that. The US government can still demand customer data from Microsoft’s European data centres simply because Microsoft is a US company. But it’s making that data much more defensible, and telling the EU that it is willing to cooperate rather than fight.
Similar over privacy. When it became clear last week that Microsoft had, quite legally, searched the emails of one of its customers concerning the theft of Microsoft IP, it knew there would be privacy issues. It immediately said two things: firstly that it would in future get a pseudo warrant from an independent lawyer who had previously been a judge, and secondly that it would include its own searches in future ‘transparency reports’ (the ones that publish the number of law enforcement searches).
It wasn’t enough for the privacy advocates who pointed to the hypocrisy of criticising NSA warrantless surveillance and then doing its own.
To Microsoft’s great credit, within a week, it has listened, heard and understood. Brad Smith announced yesterday,
Effective immediately, if we receive information indicating that someone is using our services to traffic in stolen intellectual or physical property from Microsoft, we will not inspect a customer’s private content ourselves. Instead, we will refer the matter to law enforcement if further action is required.
We’re listening: Additional steps to protect your privacy
Is this a new Microsoft — the genuinely ‘listening’ company? It no longer dominates the world’s operating systems, and is losing ground on desktop office software. But it seems to be doing one thing that none of its competitors are doing. It is listening to its customers, and giving them what they want. That alone, over the next few years, could catapult Microsoft back into a leading position.

